Following on from an earlier post about incorporating penetration testing with OWASP ZAP into an Azure DevOps pipeline, I am going to talk about how to add vulnerability checks for your ARM Templates to a release pipeline.

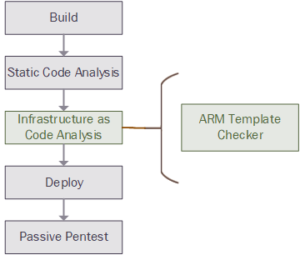
Checking the configuration of a template which deploys either PaaS or IaaS components before they are actually deployed is a great way to help prevent accidental data loss through misconfiguration, which is number 6 on the OWASP top 10 list (2017). Catching these potential issues early in the development lifecycle will also help to keep the cost of remediation down.
You need to include the GIT repository where the ARM template(s) are stored in the release as an artifact.


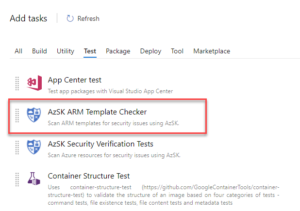
Once the ARM templates are available, you can add the validation checking to the pipeline. Microsoft have produce a wonderful tool which is easily integrated into your pipelines that is designed to check ARM Templates, the Secure DevOps Kit for Azure (AzSK). In order to use this task to your pipelines you need to install the extension from the Azure DevOps Marketplace, https://marketplace.visualstudio.com/items?itemName=azsdktm.AzSDK-task. Once you have installed this extension you should be able to add the task ‘AzSK ARM Template Checker’ to your pipeline stage.

Once you have this task its time to configure it, set the path to the folder where the ARM templates reside, and the path to the folder where the parameter files are, by selecting recursive, the task will check all template files within the folder and all child folders. If you want to exclude any templates from the scan then include these in a comma separated list in the Exclude files option.


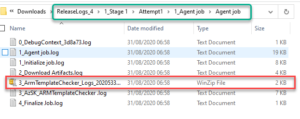
The report file from this scan is available via the download all logs from the Release pane in Azure DevOps.

![]()
The CSV file and the LOG file for the AzSK security verification test are embedded in the ‘inner’ ZIP file.

Pingback: Integrating security testing into an Azure DevOps pipeline – OWASP ZAP - John Nunn's Blog